What is an Audit Trail?
In the context of digital payments and financial infrastructure, an audit trail is a secure, immutable, and chronological record that tracks every system action, API call, and state change associated with a transaction. It provides a detailed, step-by-step history of a payment payload from the moment a customer clicks "Buy" to the final settlement or decline, definitively answering the crucial questions of who, what, when, and where an event occurred.
The Strategic Importance of Audit Trails
For enterprise engineering and finance teams, an audit trail is not just a debugging tool; it is a foundational requirement for security, compliance, and revenue optimization.
PCI DSS Compliance (Requirement 10): The Payment Card Industry Data Security Standard strictly mandates that all access to network resources and cardholder data must be logged and monitored. Without a cryptographically secure audit trail, an organization cannot achieve or maintain compliance.
Rapid Debugging: When a transaction fails, engineers need to know exactly why. Did the inbound payload fail schema validation? Did the fraud engine time out? Did the acquiring bank return a generic soft decline? A detailed audit trail pinpoints the exact point of failure in milliseconds.
Dispute Resolution: In the event of a chargeback or a complex customer support ticket, an audit trail serves as the definitive source of truth, providing cryptographic proof of authorization, 3D Secure authentication (liability shift), and payload delivery.
The Blind Spot of Monolithic Processors
Merchants relying entirely on a single, monolithic Payment Service Provider (PSP) often suffer from a severe lack of visibility. Legacy processors typically operate as "black boxes." If a transaction is declined, the PSP might only return a generic error code (e.g., "Do Not Honor"), withholding the underlying telemetry and decision-making logic.
Furthermore, if a merchant uses multiple disparate gateways without an orchestration layer, their audit trails are fragmented across half a dozen different dashboards, making holistic reporting and cross-platform debugging nearly impossible.
How Hellgate.io Centralizes Your Audit Trail
Hellgate’s Composable Payment Architecture (CPA) fundamentally believes in absolute data transparency. By sitting above your underlying processors, Hellgate centralizes and standardizes your entire payment telemetry into a single, unified audit trail.
Transparent Routing via Hub
Every time a transaction passes through the Hellgate Hub, the system logs an immutable record of the payload's journey. You can see exactly which routing rules were triggered, how the payload was manipulated (detokenized), the exact latency of the API call to the acquiring bank, and the raw webhook response returned by the processor.
Security and Vault Logs via Guardian
Hellgate Guardian maintains a strict, PCI-compliant audit trail of your sensitive data. Every time a raw Primary Account Number (PAN) is intercepted, vaulted, or resolved into a token, the action is logged. This provides your compliance team with the exact documentation required to satisfy auditors and prove that your internal systems never touched the toxic data.
Fraud Telemetry via Specter
If a transaction is blocked at the edge, Hellgate Specter logs the exact reason. Instead of a vague "Risk Declined" message, your audit trail will show the specific velocity threshold that was breached, the behavioral anomaly detected, or the IP mismatch that flagged the payload as fraudulent.
Internal Linking Strategy
Anchor Text:
immutable record of the payload's journeyTarget:
https://hellgate.io/hub(General Product Page)Context: Directs readers to learn how the Hub orchestrates transactions and records the routing telemetry.
Anchor Text:
PCI-compliant audit trail of your sensitive dataTarget:
https://hellgate.io/guardian(General Product Page)Context: Links the concept of compliant logging directly to the Guardian vault.
Anchor Text:
velocity threshold that was breachedTarget:
https://hellgate.io/specter(General Product Page)Context: Guides developers to understand how Specter logs the specific risk factors that lead to a blocked transaction.
Frequently Asked Questions (FAQ)
Can raw credit card numbers (PANs) be stored in an audit trail? Absolutely not. Under PCI DSS regulations, logging raw PANs or dynamic authentication data (like CVVs) in plain text within system logs is a catastrophic compliance violation that immediately triggers SAQ D scope and potential fines. Hellgate ensures that only safe tokens and masked data (e.g., the last 4 digits) are ever written to your logs.
How long should payment audit trails be retained? PCI DSS Requirement 10.7 mandates that audit trail history must be retained for at least one year, with a minimum of three months immediately available for analysis. Hellgate automatically manages this retention lifecycle for all data flowing through our infrastructure.
How does an audit trail help with fallback routing? If a primary acquiring bank experiences an outage and drops a transaction, the Hellgate Hub uses the audit trail to immediately recognize the failure (e.g., catching a 503 HTTP error). It then uses that real-time telemetry to trigger a dynamic fallback rule, seamlessly rerouting the payload to a secondary processor.
Stop operating in the dark.
Don't let legacy processors hide the telemetry you need to optimize your payment stack. Leverage Hellgate's Composable Payment Architecture to gain absolute visibility into your transaction flows, simplify your compliance audits, and debug failures in real-time. Explore the Hellgate Developer Docs to see our logging and webhook payloads, or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
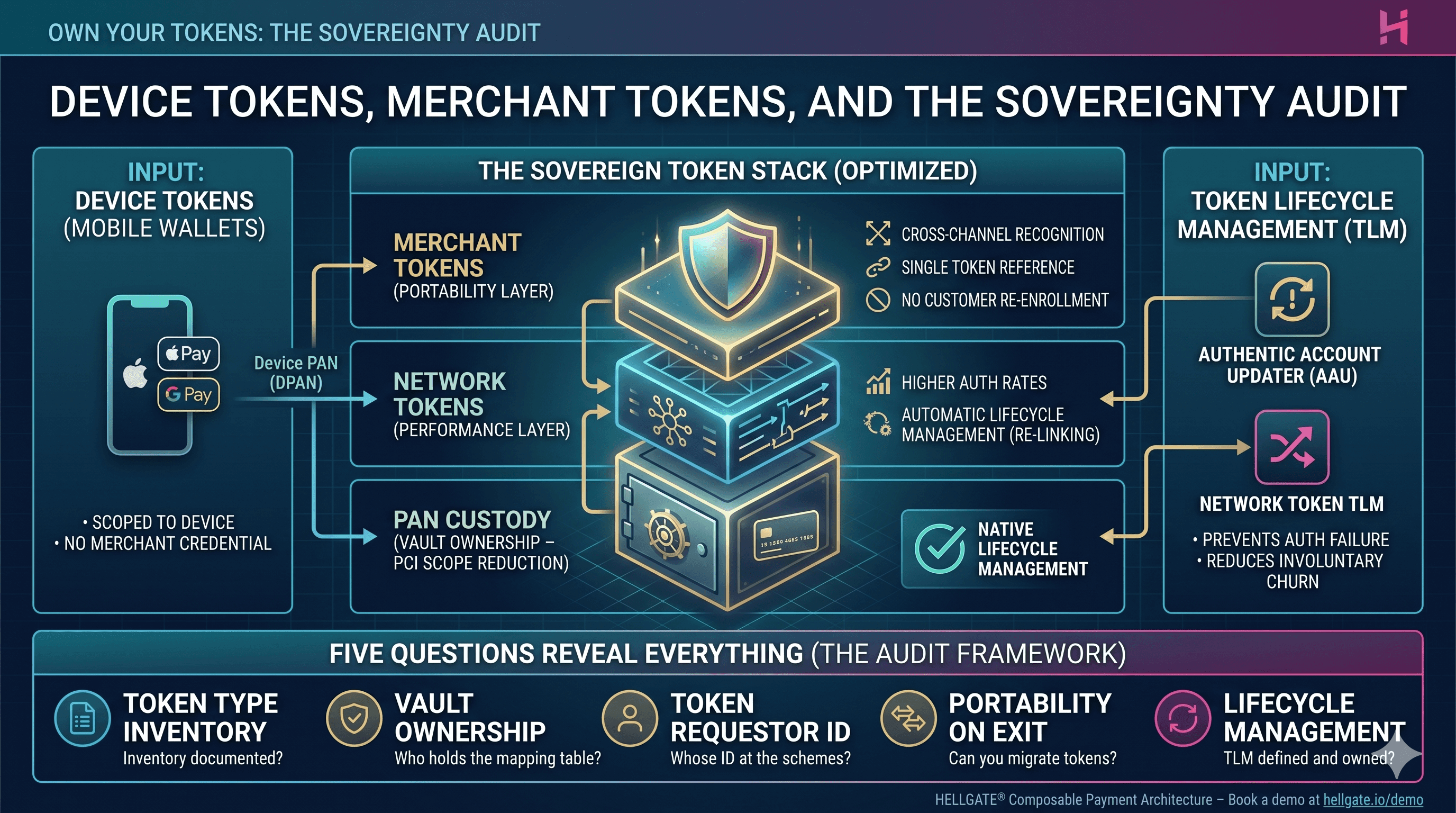
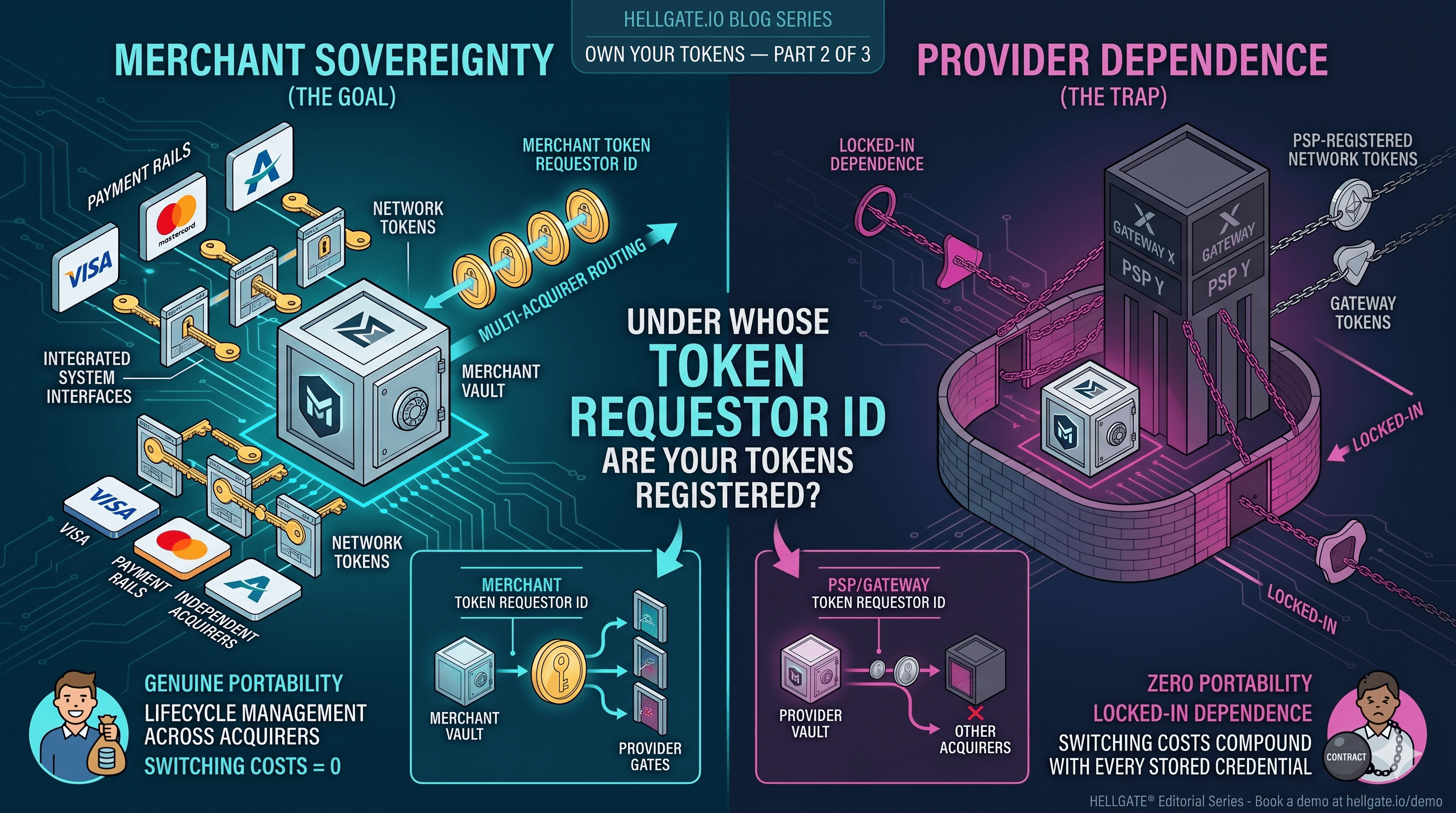
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026