What is Card Testing?
Card testing (also known as carding or account testing) is a type of automated fraud where cybercriminals use botnets to test the validity of stolen credit card credentials. By initiating thousands of small, rapid-fire transactions on a merchant's checkout page, fraudsters identify which card numbers are active and have available credit before using them for high-value unauthorized purchases elsewhere.
How Card Testing Attacks Work
Fraudsters typically acquire large lists of stolen Primary Account Numbers (PANs) from the dark web. Since many of these cards may have been canceled or reported stolen, the attacker needs to verify them.
The Target: Attackers look for checkout pages with minimal security, such as those lacking CAPTCHAs or velocity limits.
The Script: A bot script is deployed to enter card details and attempt small purchases (often $1 or less) or simple "zero-dollar" authorizations.
The Outcome: If the transaction is approved, the card is flagged as "live." If it is declined, the bot moves to the next number in the list.
The Impact on Merchants
While the individual transaction amounts are small, the aggregate damage of a card testing attack can be catastrophic for an enterprise:
Skyrocketing Authorization Fees: Merchants are charged a fee for every transaction attempt—whether approved or declined. A botnet can rack up thousands of dollars in fees in minutes.
Network Penalties: Excessive decline rates can trigger red flags with card networks (Visa, Mastercard), leading to heavy fines or being placed in "high-risk" monitoring programs.
Reputational Damage: High volumes of fraudulent traffic can cause issuing banks to lower your overall authorization rates, affecting legitimate customers.
How Hellgate.io Stops Card Testing
Hellgate’s Composable Payment Architecture (CPA) moves fraud defense to the infrastructure edge, stopping bots before they can impact your bottom line.
Edge-Level Defense with Specter
Hellgate Specter, our real-time fraud intelligence layer, is designed to identify the tell-tale patterns of card testing. Specter monitors transactional metadata in milliseconds, executing velocity checks that look for multiple rapid attempts from a single IP address, device fingerprint, or token.
Programmable Blocking via the Hub
When Specter identifies a card testing pattern, it calculates a high-risk "Specter Score." This score is instantly consumed by the Hellgate Hub, which can be programmed to:
Hard Block: Immediately drop the malicious payload at the edge, ensuring the transaction never reaches the acquirer and you incur zero authorization fees.
Step-up Challenge: Trigger a 3DS authentication challenge via Hellgate Aegis for suspicious traffic, which automated bots cannot bypass.
By decoupling fraud intelligence from the processing layer, Hellgate allows you to defend your infrastructure without introducing latency for your actual customers.
Internal Linking Strategy
Anchor Text:
real-time fraud intelligence layerTarget:
https://hellgate.io/specter(General Product Page)Context: Links the primary tool for stopping card testing to the Specter feature page.
Anchor Text:
velocity checksTarget:
https://hellgate.io/glossary/velocity-checks(Glossary Page)Context: Directs readers to a deeper explanation of the specific mechanism used to halt bot attacks.
Anchor Text:
Hellgate Hub infrastructureTarget:
https://developer.hellgate.io/(Technical Documentation)Context: Guides developers to see how to configure programmatic rules to handle high-risk fraud scores.
Frequently Asked Questions (FAQ)
Why do fraudsters use small amounts for card testing? Small transaction amounts are less likely to trigger immediate alerts for the cardholder or the bank's fraud detection systems. The goal isn't to steal the $1, but to confirm the card's validity for a much larger theft later.
Can CAPTCHA stop all card testing? While CAPTCHA can stop basic bots, sophisticated botnets can now bypass many traditional visual challenges. A more robust defense involves infrastructure-level velocity checks and device fingerprinting provided by tools like Hellgate Specter.
Does card testing happen on all payment methods? It primarily affects credit and debit cards (PAN data). However, as digital wallets and alternative payment methods grow, fraudsters are increasingly looking for ways to automate testing across various payment endpoints.
Protect your margins from automated fraud.
Don't let botnets drain your revenue through thousands of unnecessary authorization fees. Leverage Hellgate Specter to implement edge-level velocity checks and block card testing attacks in real-time. Explore the Hellgate Developer Docs to configure your fraud rules, or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
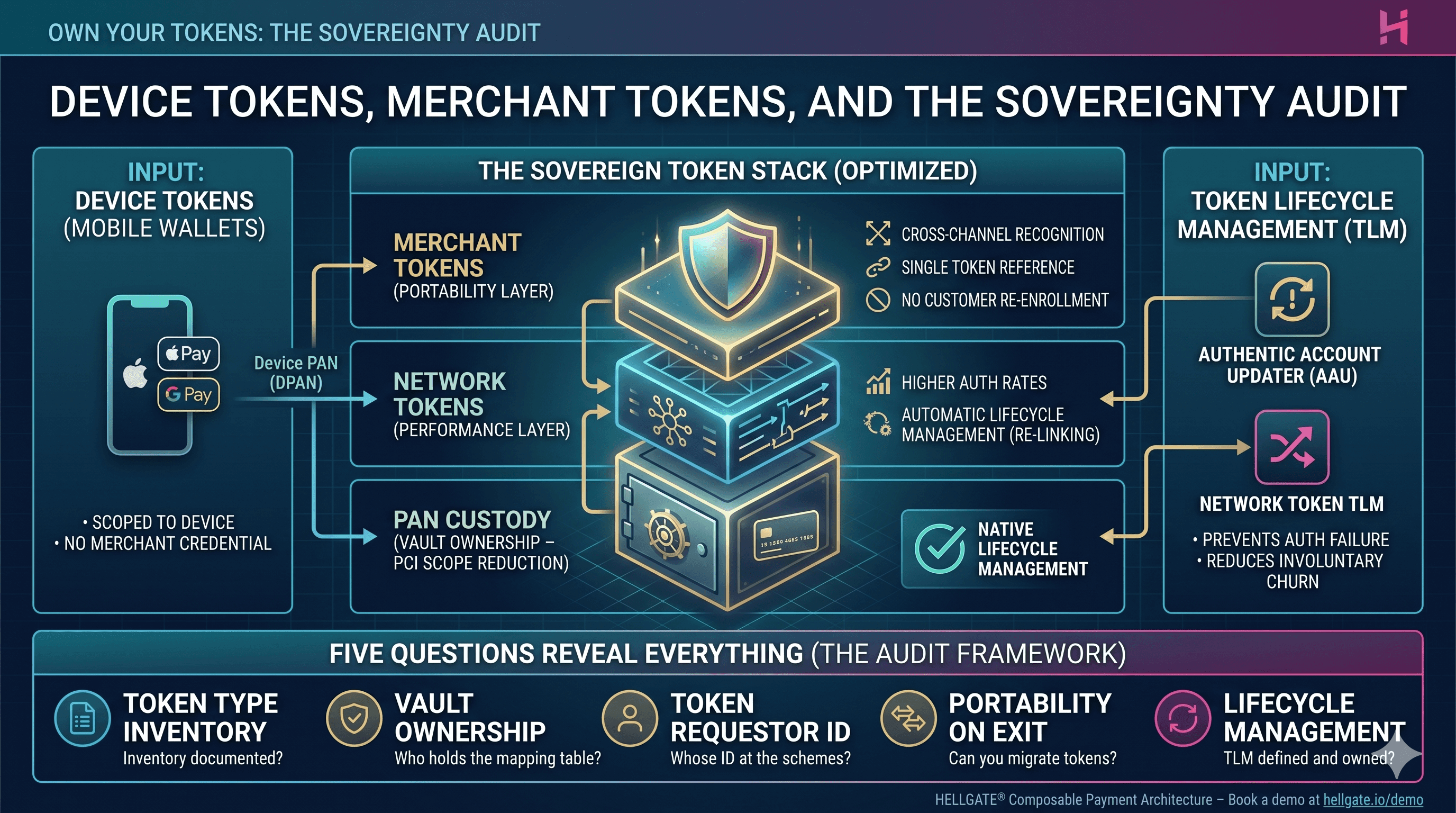
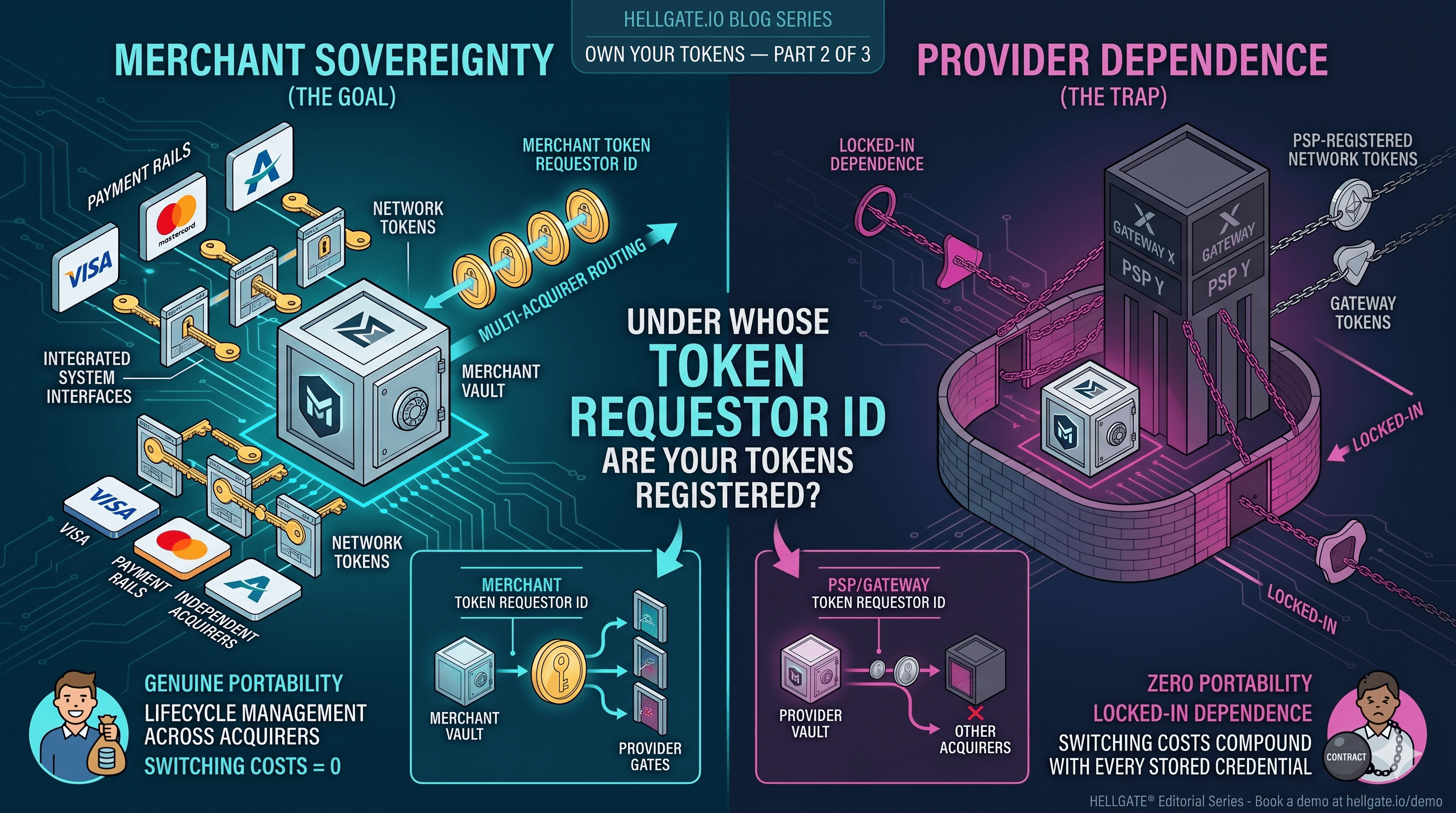
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026