What is a Cardholder Data Environment (CDE)?
The Cardholder Data Environment (CDE) is defined by the PCI Security Standards Council as the specific area of an entity's network that possesses, stores, processes, or transmits cardholder data (CHD) or sensitive authentication data (SAD). The CDE also includes any component that, if compromised, could impact the security of the cardholder data.
For any organization accepting credit card payments, the CDE is the "ground zero" of security audits. The larger and more complex your CDE, the more rigorous, expensive, and time-consuming your PCI DSS compliance requirements become.
What Components Make Up the CDE?
According to PCI DSS guidelines, the CDE is not just a single database; it is a collection of interconnected systems, including:
Network Components: Firewalls, switches, routers, and wireless access points.
Server Types: Web servers, application servers, database servers, and authentication servers.
Applications: Any internal or third-party software that handles raw Primary Account Numbers (PANs).
Virtual Machines: Any virtualized instances or containers (like Docker or Kubernetes) that process payment data.
The Cost of a Large CDE
If an enterprise utilizes a monolithic payment architecture where raw card data flows directly into their internal backend, their entire infrastructure—including their primary databases and cloud instances—is considered part of the CDE. This triggers the SAQ D compliance standard, which mandates:
Intrusive Audits: Annual on-site assessments by a Qualified Security Assessor (QSA).
Infrastructure Drag: Mandatory implementation of expensive security tools like File Integrity Monitoring (FIM) and Intrusion Detection Systems (IDS).
Engineering Opportunity Cost: Thousands of developer hours spent on security patching and compliance paperwork rather than product innovation.
How Hellgate.io Descorp-es Your CDE
Hellgate’s Composable Payment Architecture (CPA) is designed with a singular goal: to shrink your CDE to the smallest possible footprint. We achieve this through Guardian, our dedicated PCI-compliant vault and edge-proxy module.
Guardian utilizes an Edge-Proxy Interception Architecture. Instead of raw card data reaching your servers, Guardian’s inbound proxy intercepts the payment request at the network edge. It strips the raw PAN, stores it securely in the Hellgate vault, and forwards only a non-sensitive Hellgate Token to your internal environment.
By ensuring that raw cardholder data never enters your network, your internal servers are removed from the CDE. This allows you to qualify for the much simpler SAQ A standard, effectively descoping 99% of your infrastructure and liberating your engineering team from the burden of PCI audits.
Internal Linking Strategy
Anchor Text:
PCI-compliant vault and edge-proxy moduleTarget:
https://hellgate.io/guardian(General Product Page)Context: Links the method of descoping the CDE directly to Hellgate’s Guardian infrastructure.
Anchor Text:
SAQ A standardTarget:
https://hellgate.io/glossary/saq-self-assessment-questionnaire(Glossary Page)Context: Directs readers to understand the specific compliance benefits of a reduced CDE.
Anchor Text:
intercepts the payment request at the network edgeTarget:
https://developer.hellgate.io/(Technical Documentation)Context: Guides developers to the documentation to see how the proxy prevents raw data from entering their environment.
Frequently Asked Questions (FAQ)
If I use an iframe or a hosted payment page, do I still have a CDE? Yes. Even if you use an iframe, you still have a CDE, but it is significantly smaller. You are still required to validate compliance (typically via SAQ A), proving that your website cannot be tampered with to redirect data away from the secure iframe.
How does network segmentation affect the CDE? Network segmentation is the practice of isolating the CDE from the rest of a company’s network using firewalls. While this doesn't "eliminate" the CDE, it prevents the entire corporate network from being subject to PCI audits, focusing the QSA’s attention only on the segmented payment zone.
Can a CDE exist in the cloud? Absolutely. If you process payments in AWS, Azure, or Google Cloud, your cloud instances, virtual private clouds (VPCs), and storage buckets that touch card data are part of your CDE. Cloud-native tokenization via Hellgate Guardian is the most effective way to descope these cloud environments.
Shrink your CDE and scale your business.
Stop letting PCI compliance dictate your engineering roadmap. Leverage Hellgate Guardian’s edge-proxy architecture to remove raw card data from your servers and reduce your CDE to the absolute minimum. Explore the Hellgate Developer Docs to see our descoping patterns, or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
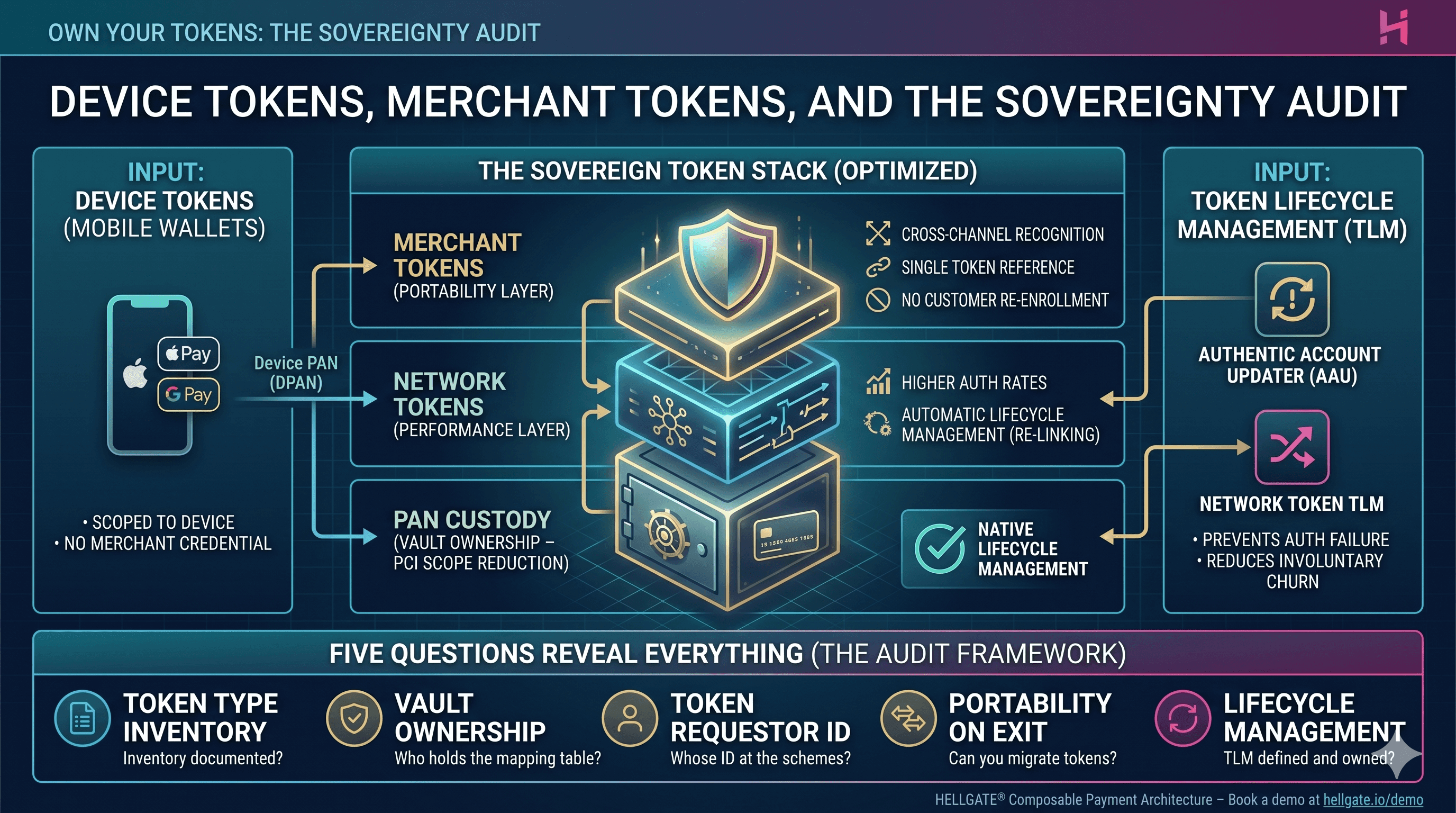
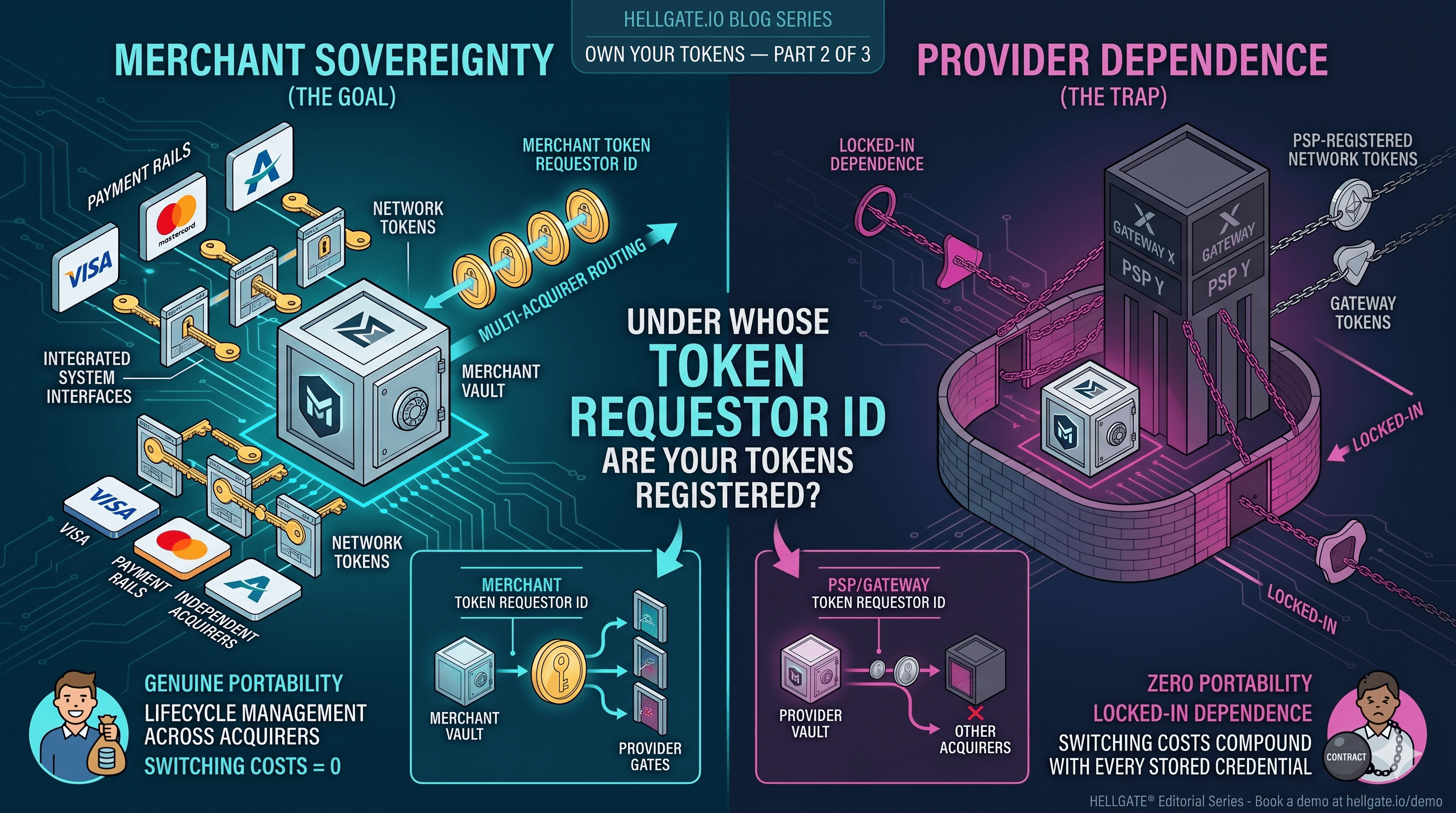
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026