What is PAN Data?
PAN Data, or Primary Account Number data, refers to the unique 14- to 19-digit number found on credit, debit, and prepaid cards. It is the most sensitive element of Cardholder Data (CHD) and serves as the primary key for identifying a cardholder's account within the global financial network. Under PCI DSS regulations, any system that stores, processes, or transmits raw PAN data is subject to the highest levels of security auditing and compliance.
The Anatomy of PAN Data
While a PAN looks like a random string of numbers, it follows a strict international standard (ISO/IEC 7812) to ensure it can be routed correctly across global networks:
Issuer Identification Number (IIN / BIN): The first 6 to 8 digits identify the card network (e.g., Visa starts with 4, Mastercard with 5) and the specific bank that issued the card.
Individual Account Identifier: The digits following the BIN are unique to the cardholder's specific account.
Checksum (Luhn Digit): The final digit is used to verify the validity of the number string via the Luhn algorithm, preventing accidental entry errors.
Why PAN Data is "Toxic" to Your Infrastructure
In the payment industry, raw PAN data is often described as "toxic." If this data resides on your internal servers or is logged in your databases, it triggers the most extensive and expensive form of PCI compliance: SAQ D.
Handling raw PAN data manually requires:
Strict Encryption: Data must be encrypted at rest and in transit using strong cryptographic keys.
Network Segmentation: Your entire network must be isolated to prevent unauthorized access to the "Cardholder Data Environment" (CDE).
Annual Audits: High-volume merchants must pay for on-site audits by a Qualified Security Assessor (QSA), which can cost hundreds of thousands of dollars and consume months of engineering time.
How Hellgate.io Secures PAN Data
Hellgate’s Composable Payment Architecture (CPA) is designed to keep raw PAN data entirely out of your systems while still allowing you to use it for transactions.
Through Guardian, our agnostic PCI-compliant vault, we utilize an Edge-Proxy Interception Architecture. When a user enters their card info on your site:
Guardian intercepts the raw PAN at the edge.
The data is instantly vaulted in our secure, dedicated infrastructure.
A non-sensitive Hellgate Token is passed to your servers.
Because your backend only ever "sees" the token and never the raw PAN data, your infrastructure is removed from the scope of PCI DSS. This allows you to qualify for the minimal SAQ A standard, saving your team from the operational burden of heavy audits while maintaining the ability to route that data to any processor via the Hellgate Hub.
Internal Verlinkungsstrategie
Anchor Text:
agnostic PCI-compliant vaultTarget:
https://hellgate.io/guardian(General Product Page)Context: Links the secure storage of PAN data to the Guardian module.
Anchor Text:
Cardholder Data Environment (CDE)Target:
https://hellgate.io/glossary/cde-cardholder-data-environment(Glossary Page)Context: Directs readers to understand the network areas affected by raw PAN data.
Anchor Text:
Edge-Proxy Interception ArchitectureTarget:
https://developer.hellgate.io/(Technical Documentation)Context: Guides developers to the technical implementation of how Hellgate strips PAN data from incoming requests.
Frequently Asked Questions (FAQ)
Can I store the first six and last four digits of a PAN? Yes. Under PCI DSS, "truncation" is allowed. Storing the first six (the BIN) and the last four digits is generally acceptable for display or identification purposes, provided the full PAN is not stored elsewhere in the same environment.
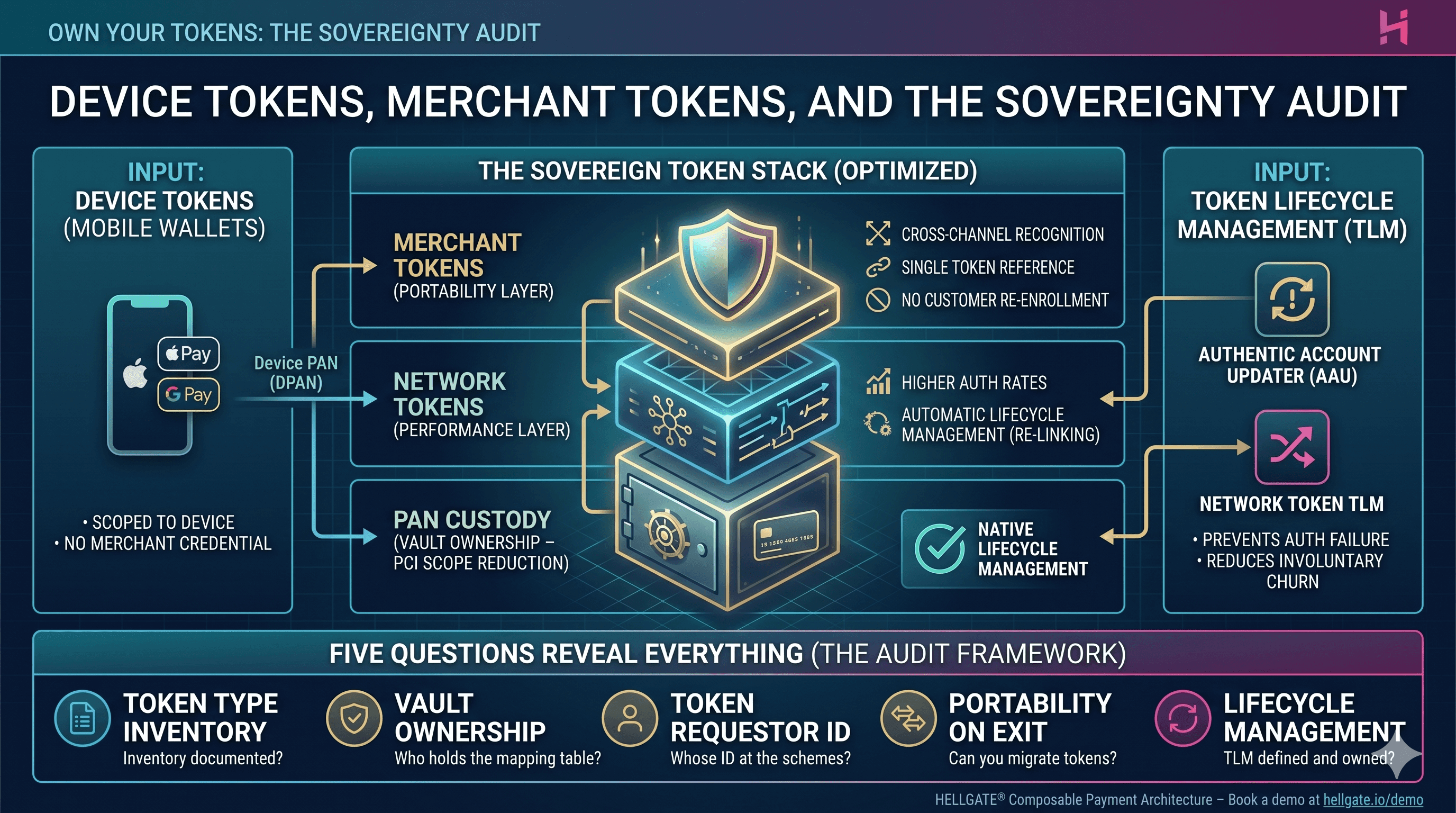
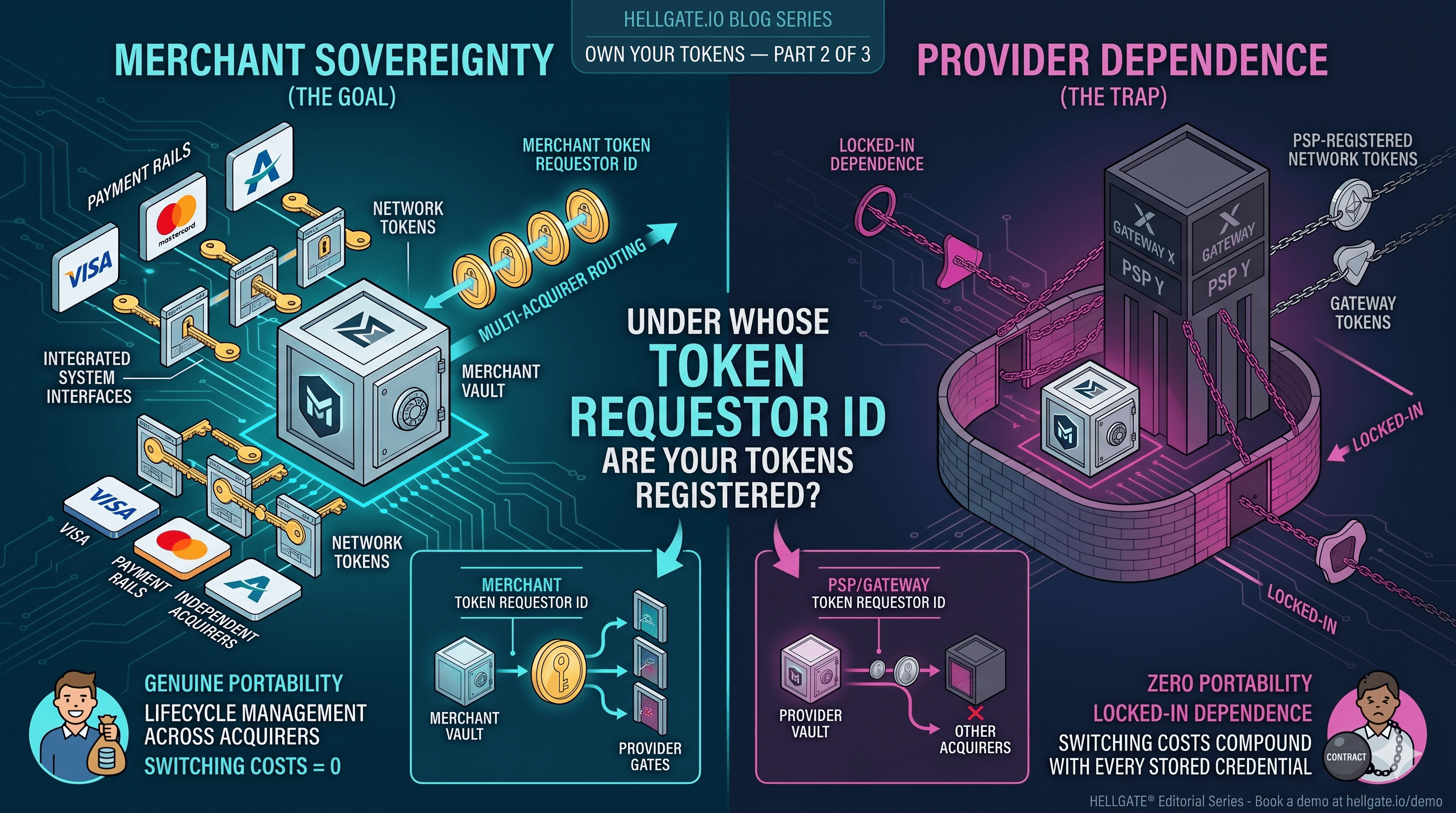
Is a Network Token the same as PAN data? No. A Network Token (like those issued by Visa or Mastercard) is a surrogate for the PAN. While it performs the same function during a transaction, it is not "toxic" in the same way because it is restricted to a specific merchant or domain, rendering it useless if stolen.
What happens if I accidentally log PAN data in my server logs? This is a common security failure. If raw PAN data is found in plain text in your logs, your systems are immediately in scope for SAQ D, and you may face significant fines or be forced to undergo a forensic audit to ensure the data has been purged and secured.
Ready to descope your payment data?
Stop letting raw PAN data create a compliance bottleneck for your engineering team. Leverage Hellgate Guardian to vault your sensitive data at the edge and reduce your PCI scope to the absolute minimum. Explore the Hellgate Developer Docs to see our tokenization flows, or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026