What is PCI DSS v4.0?
PCI DSS v4.0 is the current, active version of the Payment Card Industry Data Security Standard. Fully enforced globally by the major card networks, this standard governs the secure handling of sensitive payment account data. Version 4.0 represents the most significant overhaul of the PCI framework in a decade, shifting the industry away from a "check-the-box" annual audit mindset toward a dynamic, continuous, and zero-trust approach to data security.
The Major Shifts in Version 4.0
The transition to v4.0 was driven by the rapid evolution of cloud computing, edge networks, and increasingly sophisticated cyberattacks (such as e-commerce skimming and Magecart). Key changes that impact enterprise merchants include:
Continuous Security over Point-in-Time Compliance: Rather than preparing for a single annual assessment, organizations must now prove that security controls are operational, monitored, and effective 24/7/365.
Strict Client-Side Protections: To combat digital skimming attacks, v4.0 introduces rigorous requirements for monitoring malicious scripts on payment pages. Even merchants using iframes or redirects must now implement mechanisms to ensure the integrity of all third-party scripts loaded during checkout.
Enhanced Authentication (MFA): Multi-Factor Authentication is now strictly mandated for all access to the Cardholder Data Environment (CDE), not just for remote administrative access.
The Customized Approach: A new framework that allows advanced engineering teams to meet the objective of a requirement using modern technology (like cloud-native edge computing) rather than being forced to follow rigid, legacy prescriptive steps.
The Impact on Engineering Teams
For organizations handling raw Primary Account Numbers (PANs), v4.0 drastically increases the engineering and financial burden of maintaining SAQ D compliance. Furthermore, the updated standard has made even the simplest compliance level, SAQ A, significantly harder by introducing new script-monitoring and HTTP header validation requirements for e-commerce sites.
How Hellgate.io Simplifies v4.0 Compliance
Hellgate’s Composable Payment Architecture (CPA) is built specifically for the realities of the v4.0 era. We believe that the best way to secure your environment is to remove the sensitive data from it entirely.
Maximum Descoping via Guardian
Guardian, Hellgate’s independent PCI-compliant vault, utilizes an advanced Edge-Proxy Interception Architecture. When a customer submits a payment, Guardian intercepts the raw PAN at the network edge before it ever reaches your backend systems or client-side application state.
Guardian securely vaults the toxic data in our v4.0-compliant infrastructure and returns a non-sensitive Hellgate Token. Because your internal servers and databases only process safe tokens, your core infrastructure is entirely removed from the Cardholder Data Environment (CDE). Hellgate absorbs the complex, continuous monitoring burdens of v4.0, allowing your engineering team to focus on building your core product rather than chasing endless security patches.
Internal Linking Strategy
Anchor Text:
Cardholder Data Environment (CDE)Target:
https://hellgate.io/glossary/cde-cardholder-data-environment(Glossary Page)Context: Directs readers to understand exactly which parts of their network are affected by the new v4.0 rules.
Anchor Text:
Edge-Proxy Interception ArchitectureTarget:
https://hellgate.io/guardian(General Product Page)Context: Links the concept of descoping the new compliance burdens directly to the Guardian module.
Anchor Text:
descope your infrastructureTarget:
https://developer.hellgate.io/(Technical Documentation)Context: Guides developers to the documentation detailing how to configure the inbound proxy to achieve SAQ A compliance under the new v4.0 rules.
Frequently Asked Questions (FAQ)
Can I still validate my compliance using PCI DSS v3.2.1? No. PCI DSS v3.2.1 was officially retired on March 31, 2024. All organizations processing, storing, or transmitting cardholder data must now be fully assessed against the v4.0 standard.
Did SAQ A change in v4.0? Yes, significantly. Previously, utilizing an iframe or a hosted payment page was enough to effortlessly qualify for SAQ A. Under v4.0, SAQ A merchants must implement strict controls to detect unauthorized changes to the payment page scripts (Requirement 6.4.3) and protect against HTTP header manipulation (Requirement 11.6.1).
What is the difference between the Prescriptive Approach and Customized Approach? The Prescriptive Approach dictates exactly how a security control must be implemented (e.g., "Passwords must be changed every 90 days"). The Customized Approach allows organizations to implement alternative technologies that achieve the same security objective, provided they complete a rigorous, targeted risk analysis to prove the custom control is effective.
Stop chasing compliance. Start orchestrating payments.
Don't let the strict new requirements of PCI DSS v4.0 drain your engineering resources. Leverage Hellgate Guardian to intercept and vault your sensitive data at the edge, drastically reduce your PCI scope, and scale your global payments effortlessly. Explore the Hellgate Developer Docs to see our compliance-descoping tools, or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
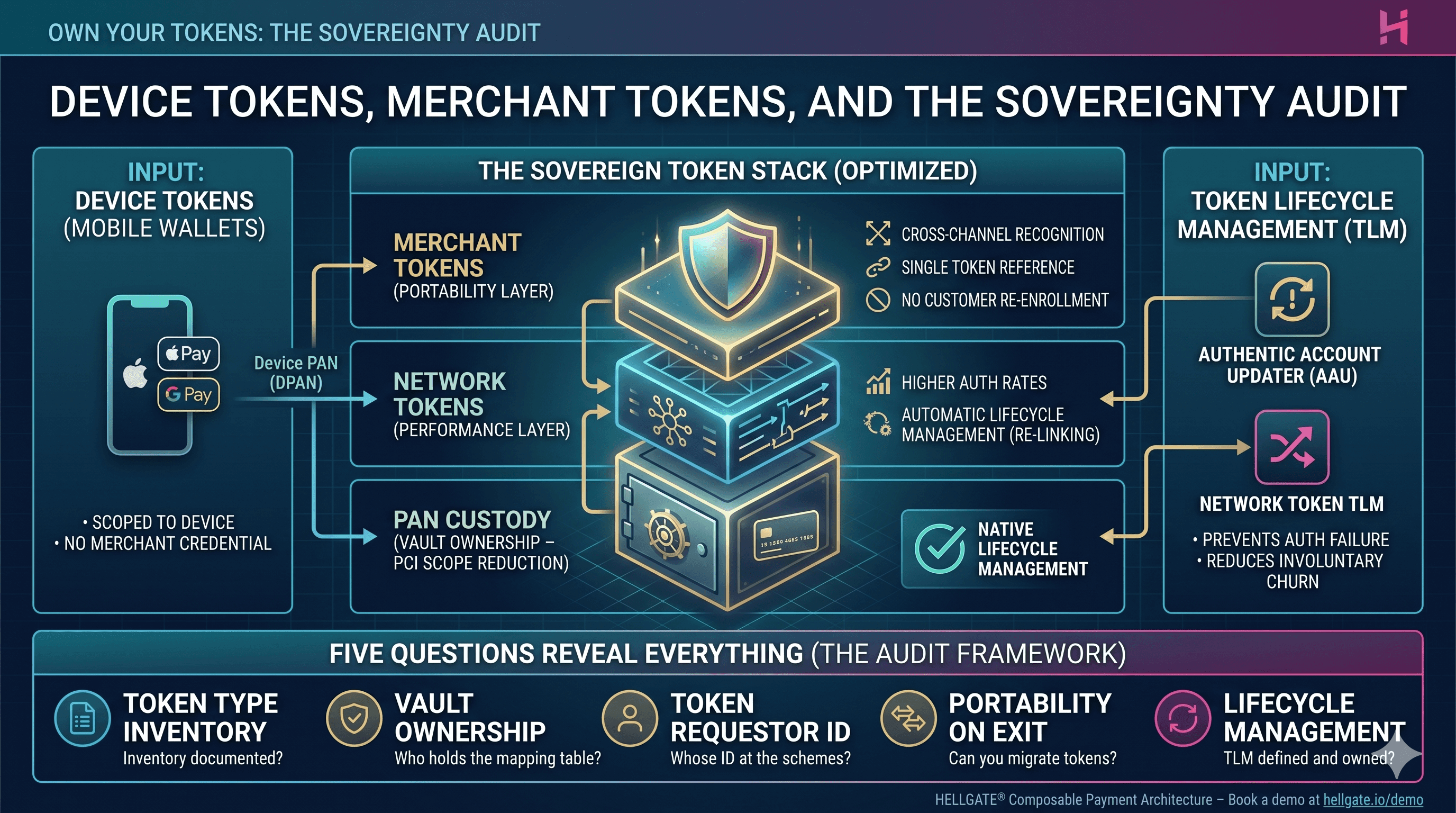
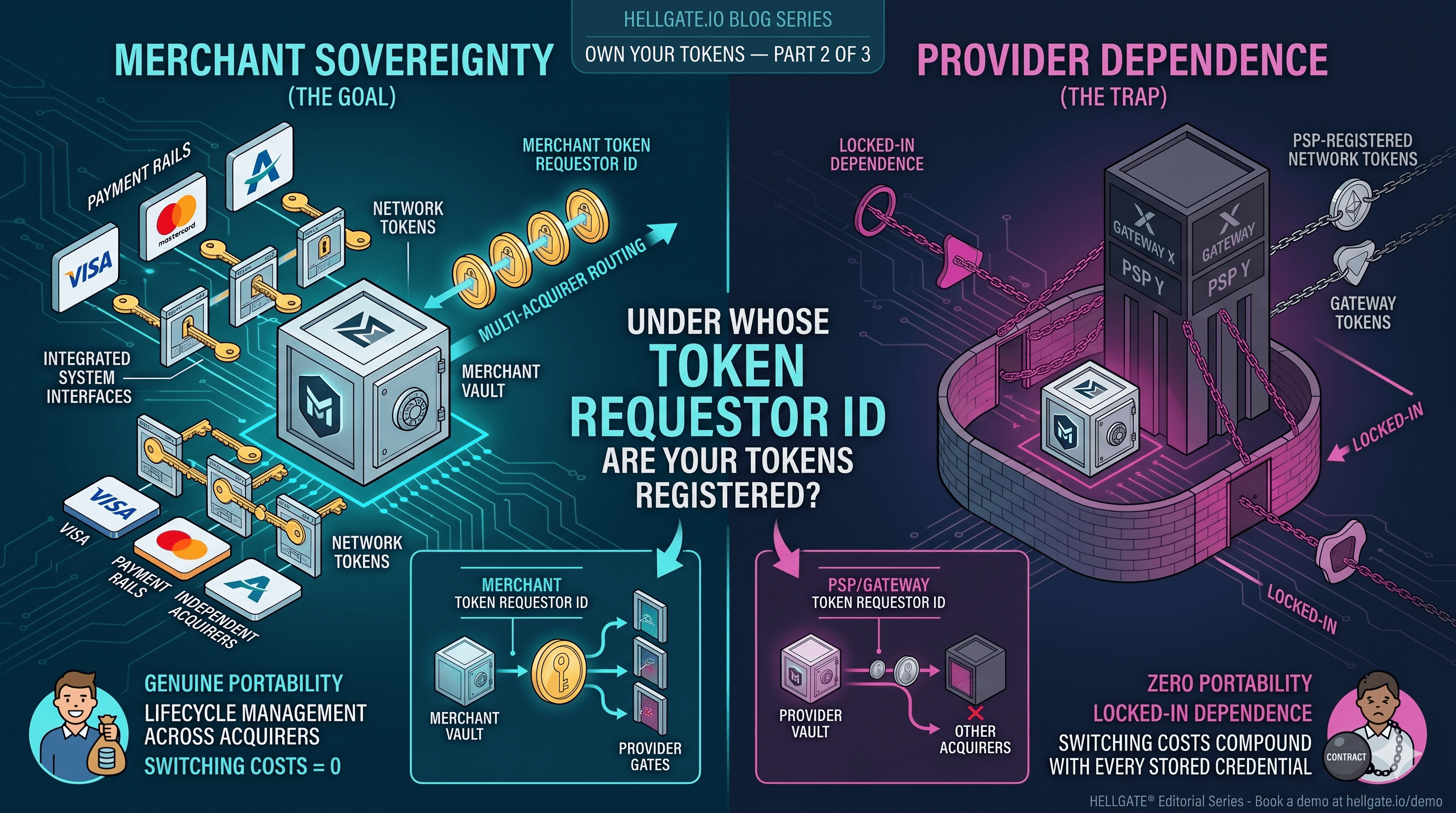
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026