What is an SAQ (Self-Assessment Questionnaire)?
A Self-Assessment Questionnaire (SAQ) is a mandatory compliance validation tool used by merchants to evaluate and report their adherence to the Payment Card Industry Data Security Standard (PCI DSS). The specific SAQ tier a merchant is required to complete depends entirely on their payment architecture and how their systems capture, store, and transmit sensitive Primary Account Numbers (PANs).
Understanding SAQ Types and the Compliance Burden
For enterprise Chief Technology Officers (CTOs), managing PCI DSS compliance is often viewed as a persistent operational drag. Handling raw payment credentials on internal infrastructure triggers the highly complex and expensive SAQ D standard.
Falling under the SAQ D classification forces development teams into endless cycles of security patching and audit preparation. It requires merchants to implement mandatory file integrity monitoring, execute complex network segmentation, and undergo highly expensive annual on-site audits conducted by Qualified Security Assessors (QSAs). This compliance nightmare severely restricts an engineering team's capacity to build revenue-generating features.
How Hellgate.io Reduces Your SAQ Scope
Hellgate solves the data hostage paradox and drastically reduces compliance overhead through the Composable Payment Architecture (CPA). The foundational keystone of this ecosystem is Guardian, a highly specialized, fully PCI-compliant vault and tokenization module delivered as managed, dedicated infrastructure.
Guardian physically and legally decouples data storage from data processing. It achieves this through a sophisticated Edge-Proxy Interception Architecture. When a consumer submits their payment details, Guardian's Inbound Proxy intercepts the HTTP request at the edge. It strips the raw PAN from the payload, securely stores it within the dedicated vault, generates a non-sensitive Hellgate Token, and forwards only this safe token to the merchant's backend servers.
Because the merchant's internal infrastructure never touches, processes, or stores the raw PAN, their compliance burden is instantly reduced from the highly complex and expensive SAQ D standard to the minimal SAQ A standard. This architectural shift instantly descopes the environment, returning thousands of hours of engineering capacity back to your team.
Internal Linking Strategy
Anchor Text:
PCI-compliant vault and tokenization moduleTarget:
https://hellgate.io/cpa/guardian(Product Page)Context: Links the concept of reducing SAQ requirements directly to the Guardian infrastructure module.
Anchor Text:
Composable Payment Architecture (CPA)Target:
https://hellgate.io/cpa(General Product Page)Context: Directs readers to understand how decoupled infrastructure aids in compliance.
Anchor Text:
Edge-Proxy Interception ArchitectureTarget:
https://developer.hellgate.io/(Technical Documentation)Context: Guides developers to the documentation on how to implement the inbound and outbound proxy to achieve SAQ A compliance.
Frequently Asked Questions (FAQ)
What is the difference between SAQ A and SAQ D?
SAQ A is the simplest questionnaire, reserved for merchants who have fully outsourced all cardholder data functions to validated third parties, meaning raw PANs never touch their internal servers. SAQ D is the most exhaustive questionnaire, required for merchants who directly store, process, or transmit raw credit card data on their own infrastructure, triggering strict security and auditing mandates.
Does using a tokenization service completely eliminate the need for an SAQ?
No. Any merchant that accepts credit card payments must maintain and validate PCI compliance. However, utilizing an advanced proxy and vaulting solution ensures you only have to complete the minimal SAQ A standard, rather than the burdensome SAQ D.
How does Guardian securely route payments if I only have a token? Through its Outbound Proxy. When your orchestration engine needs to authorize a payment, the request containing the safe token is routed out through Guardian. Guardian resolves the token in real-time, injects the raw PAN into the payload, and transmits it directly to the target Payment Service Provider, allowing you to route transactions without bringing your core systems into PCI scope.
Stop wasting engineering hours on PCI audits.
Liberate your development team from the endless cycle of SAQ D compliance. Leverage Hellgate Guardian's edge-proxy architecture to vault raw data independently, drop your compliance scope to SAQ A, and regain control over your payment stack. Explore the Hellgate Developer Docs to see how easily you can implement our proxy interceptors, or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
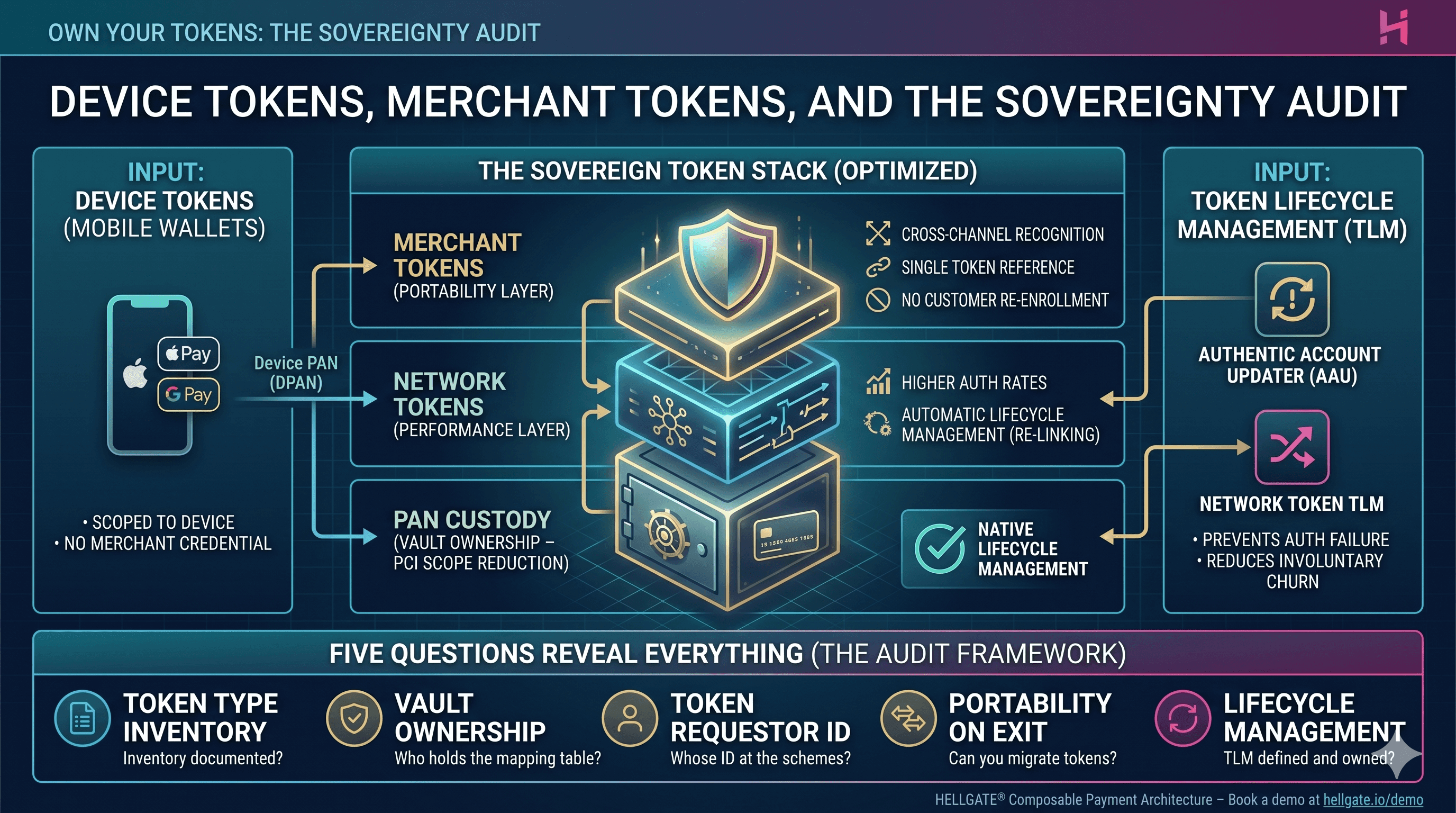
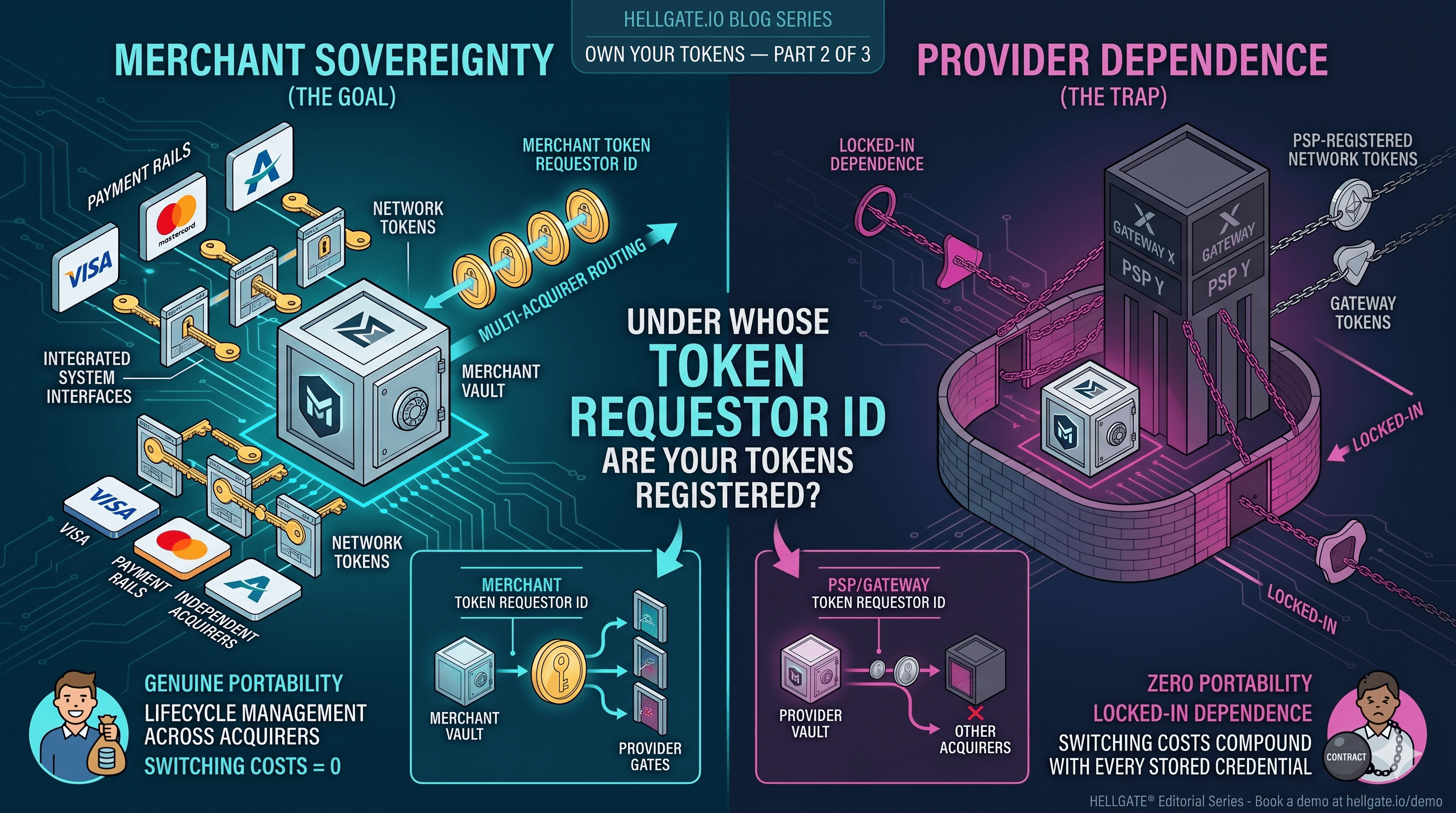
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026