What is Scope Reduction?
In enterprise payments and cybersecurity, scope reduction (often referred to as PCI descoping) is the architectural strategy of deliberately minimizing the number of system components, people, and processes that interact with, transmit, or store raw Cardholder Data (such as the Primary Account Number or PAN).
Because the Payment Card Industry Data Security Standard (PCI DSS) applies strictly to the Cardholder Data Environment (CDE), actively reducing the size and footprint of that environment is the most effective way for a merchant to slash compliance costs, minimize engineering overhead, and shrink their attack surface against cyber threats.
The Crushing Burden of a Large Scope
If an enterprise allows a raw 16-digit credit card number to pass through its internal web servers, application logs, or backend databases, their entire infrastructure is "in scope." This triggers the punishing SAQ D compliance level.
Managing an SAQ D environment requires an exhausting amount of resources, including:
Strict Network Segmentation: Building complex firewalls to isolate the CDE from the rest of the corporate network.
Rigorous Vulnerability Management: Enforcing aggressive, 30-day patching schedules that interrupt standard feature development.
Expensive Audits: Hiring external Qualified Security Assessors (QSAs) for deep, annual penetration testing and compliance validation.
True scope reduction is not about building higher walls around this toxic data; it is about ensuring the data never enters your environment in the first place.
How Hellgate.io Engineers Ultimate Scope Reduction
Hellgate’s Composable Payment Architecture (CPA) fundamentally eliminates your compliance burden by physically decoupling your infrastructure from the raw payment data. We execute complete scope reduction at the network edge.
Edge-Proxy Interception via Guardian
The most reliable way to reduce your PCI scope is to utilize an independent vault. Hellgate Guardian acts as a secure, edge-proxy shield between your customers and your backend servers. When a user submits their payment details on your checkout page, Guardian intercepts the HTTP payload in flight.
Guardian securely extracts and vaults the raw PAN within Hellgate's Level 1 PCI-certified infrastructure, dynamically replacing it with a benign Hellgate Token. By the time the payload reaches your internal servers, the toxic data is gone.
The SAQ A Advantage
Because your internal databases and APIs only ever receive, store, and transmit mathematically irreversible tokens, your infrastructure is entirely removed from the CDE. This aggressive scope reduction qualifies your enterprise for SAQ A—the absolute lowest level of PCI compliance. Your engineering team avoids the crushing maintenance of SAQ D, while still retaining the ability to process seamless, one-click checkouts and recurring subscriptions.
Internal Linking Strategy
Anchor Text:
Cardholder Data Environment (CDE)Target:
/glossary/cde-cardholder-data-environment(Glossary Page)Context: Directs readers to understand exactly what systems are regulated by PCI DSS when raw data is present.
Anchor Text:
edge-proxy shieldTarget:
/guardian(General Product Page)Context: Links the tactical execution of scope reduction directly to the Guardian interception module.
Anchor Text:
SAQ ATarget:
/glossary/saq-a(Glossary Page)Context: Guides developers to understand the specific, minimized compliance questionnaire they qualify for after utilizing Hellgate Guardian.
Frequently Asked Questions (FAQ)
What is the difference between scope reduction and network segmentation? Network segmentation is a tactic used to achieve scope reduction. By placing firewalls between the systems that touch card data and those that don't, you reduce the overall size of the CDE. However, using an edge-proxy tokenization vault like Hellgate Guardian is a much more powerful form of scope reduction, as it removes the CDE from your internal network entirely.
Do tokens completely eliminate my need to be PCI compliant? No. If you accept credit cards, you must be PCI compliant. However, scope reduction drastically changes how you comply. By using tokens and an edge proxy, you reduce your compliance requirement from a massive, 300+ question audit (SAQ D) down to a simple, short self-assessment regarding basic security hygiene like strong passwords and vendor management (SAQ A).
Can client-side encryption (like Stripe Elements or Adyen Drop-in) reduce my scope? Yes. Client-side iframes and encryption libraries are designed to capture the PAN directly from the user's browser, bypassing your servers to achieve SAQ A. However, using a legacy PSP's iframe locks your data into their proprietary vault. Hellgate Guardian provides the exact same scope reduction, but issues an agnostic token that you can route anywhere.
Scale your payments, not your compliance overhead.
Stop burning valuable engineering cycles managing firewalls, patching servers, and preparing for grueling SAQ D audits. Leverage Hellgate's Composable Payment Architecture to intercept raw data at the edge, aggressively reduce your PCI scope, and reclaim your development resources.
Would you like me to generate a checklist comparing the engineering requirements of an SAQ D environment versus an SAQ A environment utilizing Hellgate Guardian? Or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
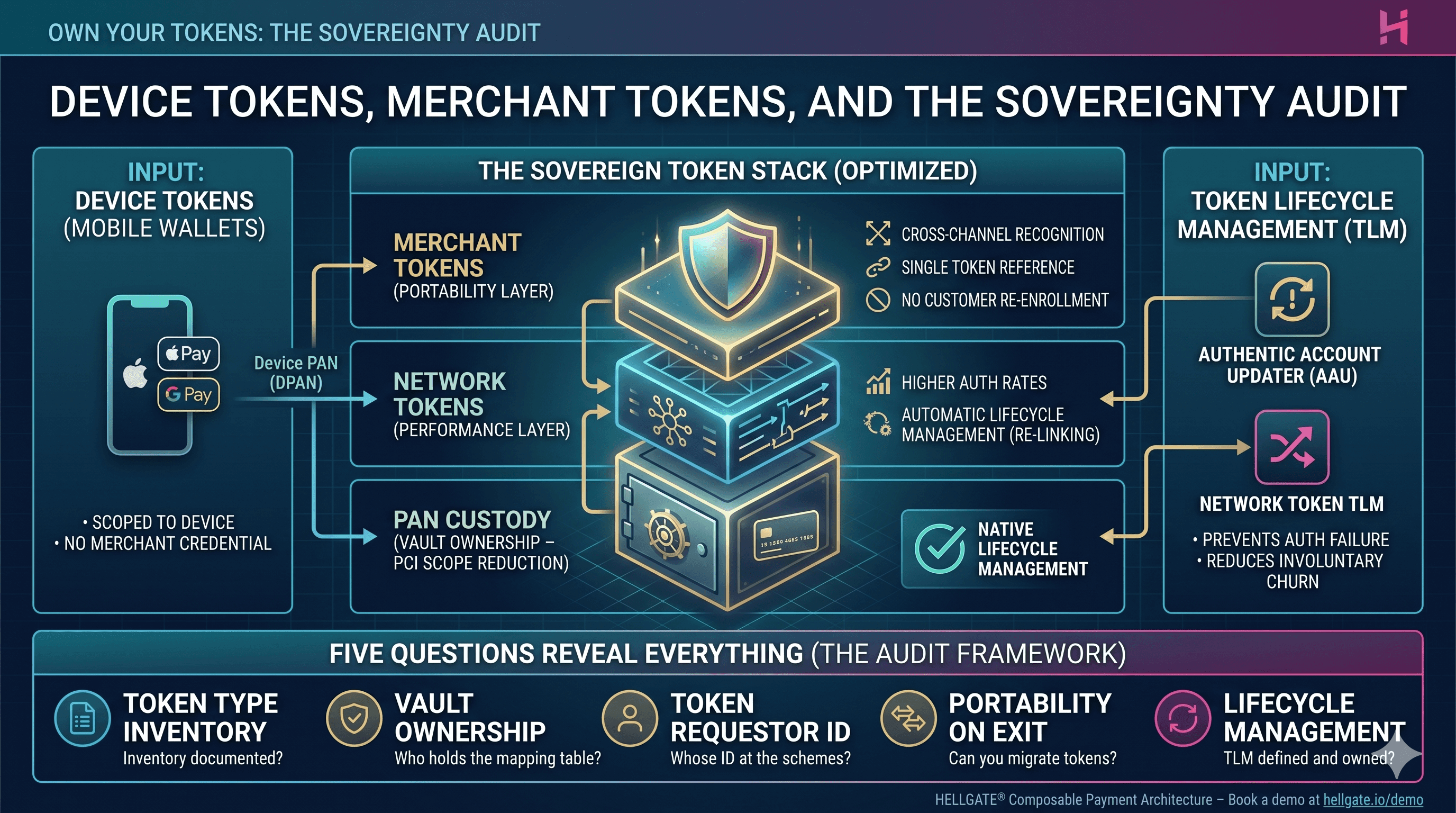
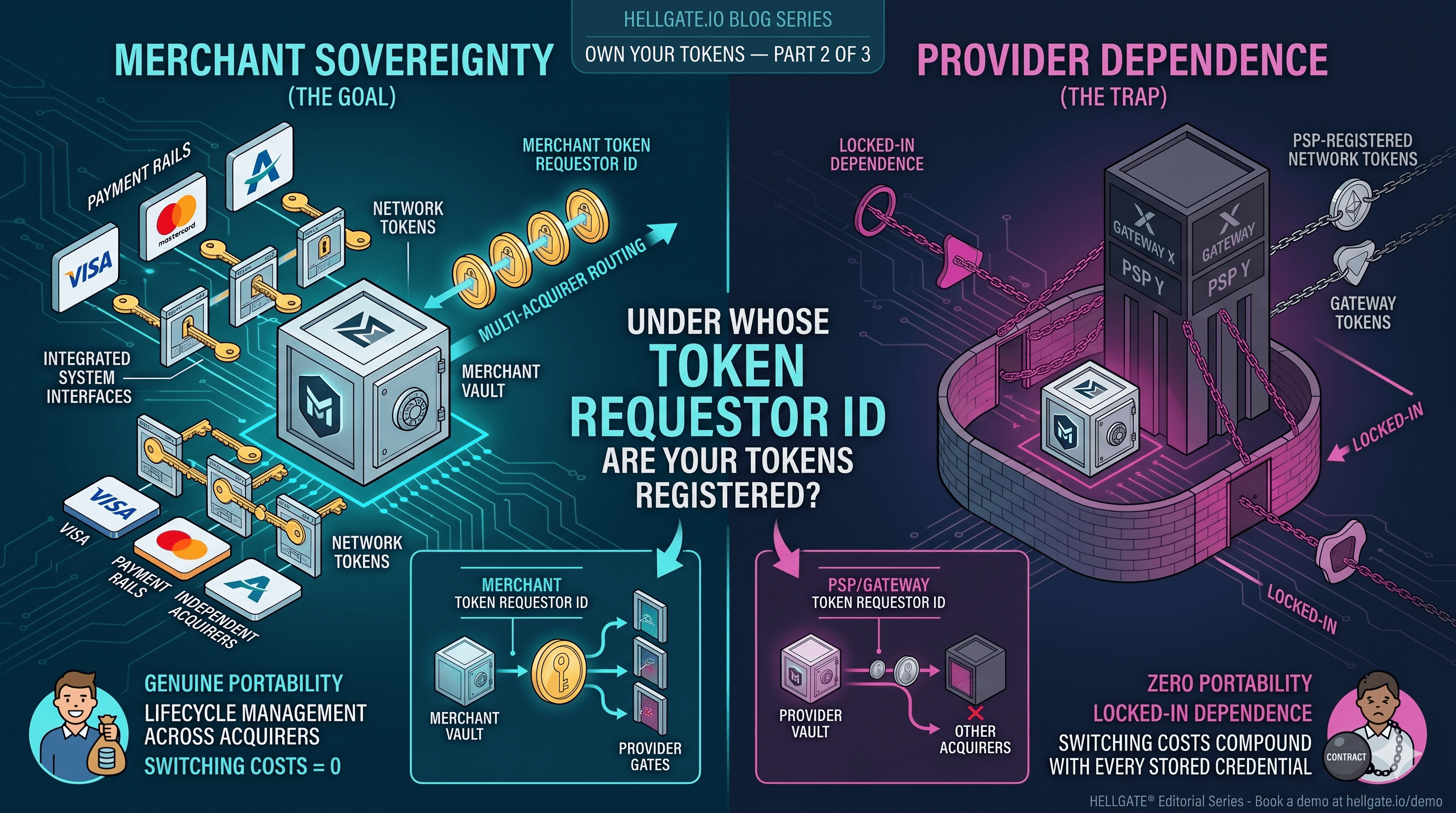
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026