What is a Stripe Token?
A Stripe Token (traditionally seen as a string starting with tok_, or in modern integrations as a PaymentMethod object) is a secure, proprietary surrogate value generated by Stripe's client-side libraries (like Stripe.js or Stripe Elements). It represents a customer's highly sensitive payment information—such as a credit card number or bank account—allowing merchants to process transactions without ever exposing their own servers to the raw data.
How Stripe Tokens Work (and the PCI Benefit)
When an enterprise integrates Stripe for checkout, they typically embed Stripe's secure iframes (Elements) onto their payment page.
Capture: The customer types their Primary Account Number (PAN) directly into the Stripe-hosted iframe.
Tokenization: Stripe intercepts the raw data, securely vaults it in their proprietary databases, and instantly returns a Stripe Token to the merchant's frontend application.
Authorization: The merchant passes this benign token to their own backend servers, which then use it to make an API call to Stripe to capture the funds.
Because the raw credit card data bypasses the merchant's servers entirely, the merchant's infrastructure qualifies for the lowest level of PCI compliance (SAQ A). This is a massive engineering benefit.
The Strategic Danger: Vendor Lock-In
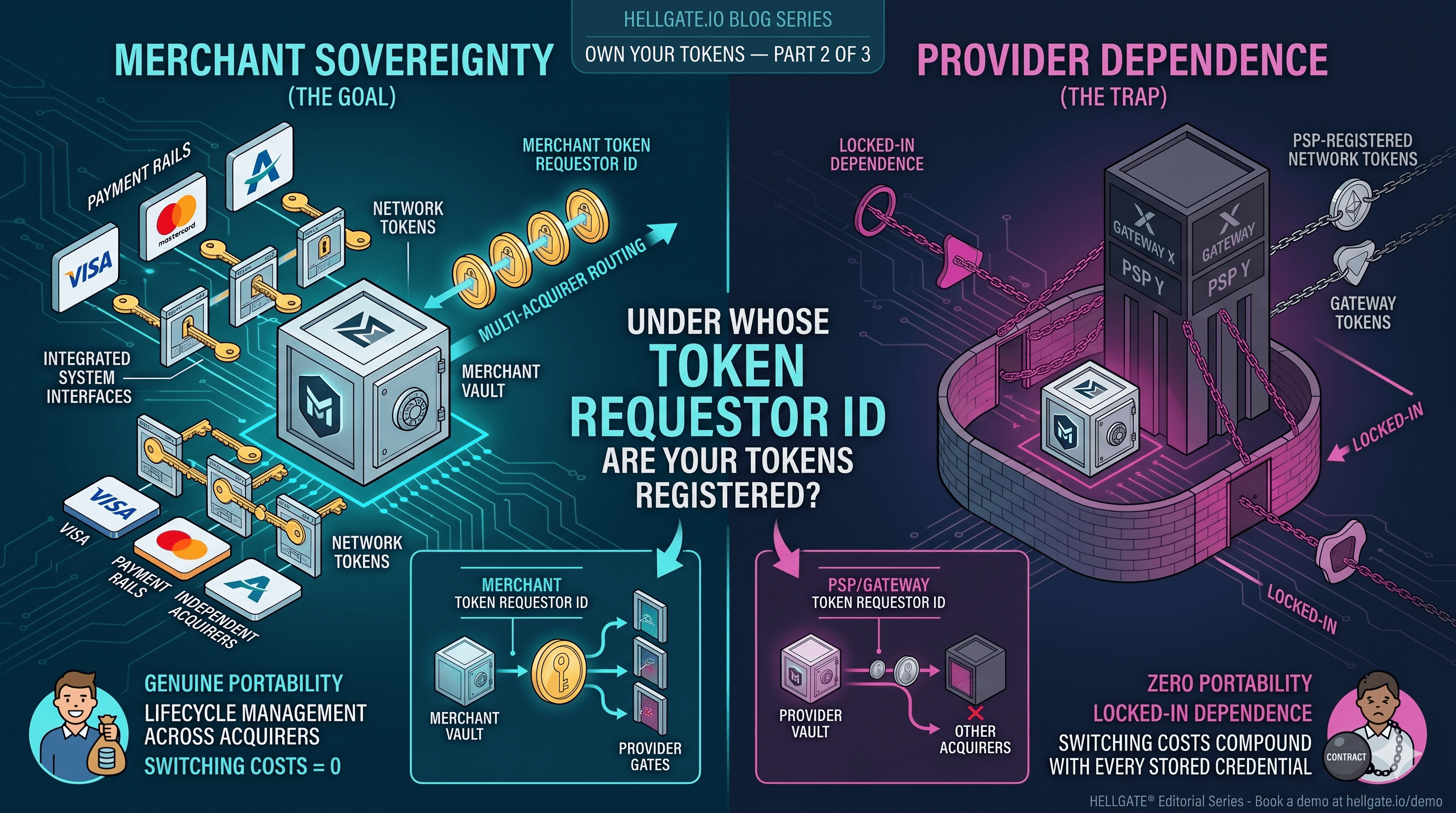
While Stripe provides an excellent developer experience, building your recurring revenue business entirely on Stripe Tokens creates a severe strategic vulnerability: Vendor Lock-in.
A Stripe Token is mathematically and systemically bound to the Stripe ecosystem. It is proprietary. You cannot take a tok_12345 and send it to Adyen, Braintree, or a localized European acquiring bank to process a payment.
If your enterprise scales globally and you realize a local processor offers 2% higher authorization rates in Latin America, or if Stripe unilaterally raises its processing fees, your data is trapped. To leave, you must initiate a complex, month-long legal and technical process known as a "PCI-to-PCI migration" to extract the underlying raw PANs.
How Hellgate.io Breaks the Lock-In
Hellgate’s Composable Payment Architecture (CPA) gives you the exact same PCI SAQ A benefits as Stripe Elements, but with absolute data sovereignty and routing freedom.
Agnostic Vaulting via Guardian
Instead of vaulting your customers' cards inside Stripe's walled garden, you utilize Hellgate Guardian. Guardian uses an edge-proxy architecture to intercept the raw PAN at checkout. It vaults the data independently and issues a universally portable Hellgate Token. Your servers remain completely out of scope.
Dynamic Detokenization via Hub
Because you own the Hellgate Token, you dictate where the transaction goes. If you want to process a payment through Stripe, the Hellgate Hub intercepts your API request, dynamically detokenizes the payload, and seamlessly provisions the data to Stripe on the fly.
If Stripe experiences an outage, or if a transaction is better suited for a different gateway, the Hub instantly routes that exact same Hellgate Token to your backup processor. You get the world-class processing power of Stripe when you want it, without being held hostage by their proprietary tokens.
Internal Linking Strategy
Anchor Text:
Vendor Lock-inTarget:
https://hellgate.io/glossary/data-portability(Glossary Page)Context: Directs readers to learn more about the strategic dangers of proprietary tokens and the value of true data portability.
Anchor Text:
vaults the data independentlyTarget:
https://hellgate.io/guardian(General Product Page)Context: Links the solution of an agnostic, edge-proxy vault directly to the Guardian module.
Anchor Text:
dynamically detokenizes the payloadTarget:
https://hellgate.io/glossary/detokenization(Glossary Page)Context: Guides developers to understand how the Hub safely swaps tokens for raw data in flight to communicate with gateways like Stripe.
Frequently Asked Questions (FAQ)
Are Stripe PaymentMethods the same as Stripe Tokens? Functionally, yes. Stripe introduced PaymentMethod and PaymentIntent objects as a modernized, SCA-compliant upgrade to their legacy tok_ objects. While they support more complex payment flows (like 3D Secure and local payment methods), they suffer from the exact same fundamental vendor lock-in. They only work on Stripe.
Can I export my Stripe Tokens? You cannot export the tokens themselves, as they are meaningless outside of Stripe's API. You can request a "PCI-to-PCI migration," where Stripe securely transfers the underlying raw credit card numbers to a new PCI-compliant Level 1 provider (like Hellgate Guardian).
Does Hellgate replace Stripe? No. Hellgate sits above Stripe as an orchestration and independent vaulting layer. Many of our enterprise clients route millions of dollars through Stripe daily. Hellgate simply ensures that the merchant retains ownership of the credential, allowing them to route to Stripe alongside other global acquirers.
Build your business on tokens you actually own.
Stop letting legacy processors hold your vaulted customers hostage. Leverage Hellgate's Composable Payment Architecture to vault your data independently, achieve SAQ A compliance, and route your transactions to Stripe or any other gateway with total freedom. Explore the Hellgate Developer Docs to see our agnostic tokenization API, or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
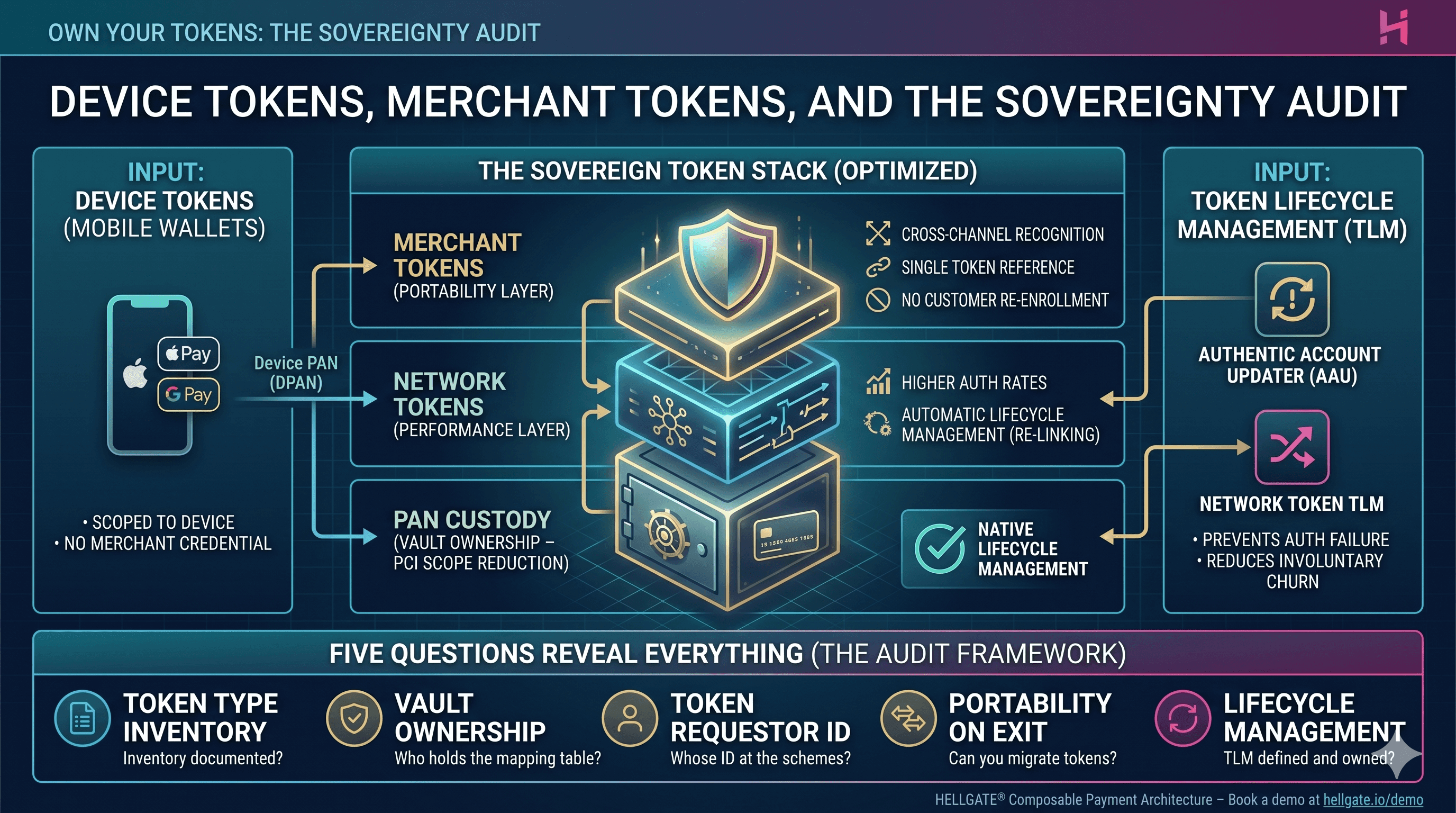
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026