What is Vulnerability Management?
In the context of enterprise payments and cybersecurity, vulnerability management is the continuous, cyclical process of identifying, classifying, prioritizing, remediating, and mitigating software vulnerabilities and security gaps within an organization's IT infrastructure. It is a foundational pillar of protecting sensitive customer data from cyberattacks and is strictly mandated by industry regulations like PCI DSS.
The Weight of the Cardholder Data Environment (CDE)
If your enterprise architecture allows raw Primary Account Numbers (PANs) to touch your internal servers, databases, or application logs, your entire network is designated as part of the Cardholder Data Environment (CDE). This triggers the incredibly demanding SAQ D compliance standard, turning vulnerability management into a massive operational drag for your engineering team.
Under strict PCI DSS requirements, managing vulnerabilities in a CDE involves:
Aggressive Patch Management: Critical security patches (such as those addressing zero-day CVEs) must be deployed within 30 days of release. This often forces engineering teams to take systems offline and pause feature development.
Continuous Scanning: Internal and external vulnerability scans must be run quarterly, and after any significant network change, by an Approved Scanning Vendor (ASV).
Penetration Testing: Expensive, manual penetration testing must be conducted annually at both the network and application layers to actively exploit potential weaknesses.
Client-Side Script Monitoring: Under the new PCI DSS v4.0 standards, merchants must actively monitor and manage the vulnerabilities of all third-party JavaScript running on their payment pages to prevent digital skimming (Magecart) attacks.
How Hellgate.io Offloads the Burden
Hellgate’s Composable Payment Architecture (CPA) fundamentally changes your security posture. We believe the most effective way to manage the vulnerabilities associated with a Cardholder Data Environment is to remove your infrastructure from the CDE entirely.
Total Descoping via Guardian
Hellgate Guardian acts as your independent, edge-proxy vault. When a customer initiates a payment, Guardian intercepts the HTTP payload at the network edge, stripping out the raw PAN before it ever hits your backend servers. Guardian securely vaults the sensitive data within Hellgate's fully managed, PCI Level 1 certified infrastructure and returns a benign Hellgate Token.
Engineering Freedom
Because your internal servers only ever process and store non-sensitive tokens, your infrastructure's compliance scope drops to the minimal SAQ A standard. While you still must maintain basic security hygiene, the crushing burden of CDE-level vulnerability management—the aggressive patching schedules, ASV scanning, and deep penetration testing—is completely offloaded to Hellgate's dedicated security teams. Your engineers get to go back to building your core product.
Internal Linking Strategy
Anchor Text:
Cardholder Data Environment (CDE)Target:
/glossary/cde-cardholder-data-environment(Glossary Page)Context: Directs readers to understand exactly which parts of their network are affected by strict patching rules.
Anchor Text:
PCI DSS v4.0Target:
/glossary/pci-dss-v4-0(Glossary Page)Context: Links the concept of vulnerability management directly to the new, rigorous requirements for client-side script monitoring.
Anchor Text:
independent, edge-proxy vaultTarget:
/guardian(General Product Page)Context: Guides developers to understand how the Guardian module intercepts data to shrink their attack surface and offload security maintenance.
Frequently Asked Questions (FAQ)
What is the difference between vulnerability scanning and penetration testing? Vulnerability scanning is an automated, high-level process that checks systems against a database of known flaws (like outdated software versions or missing patches). Penetration testing is a manual, targeted exercise where ethical hackers actively attempt to exploit those vulnerabilities to see how deeply they can breach your network.
What is a CVE? CVE stands for Common Vulnerabilities and Exposures. It is a public glossary of known cybersecurity vulnerabilities. When a new flaw in a web server or database is discovered, it is assigned a CVE ID and a severity score (CVSS). PCI compliance dictates how quickly you must patch high-scoring CVEs in your payment environment.
Does SAQ A compliance require vulnerability management? Yes, but the scope is drastically reduced compared to SAQ D. If you use Hellgate Guardian to achieve SAQ A, your vulnerability management efforts shift away from deep server-level patching and focus primarily on securing the web server that hosts the checkout page, implementing strong passwords, and monitoring third-party scripts.
Stop wasting engineering cycles on server patching.
Don't let the crushing weight of SAQ D vulnerability management drain your development resources and inflate your operational costs. Leverage Hellgate's Composable Payment Architecture to intercept sensitive data at the edge, drastically shrink your attack surface, and offload your compliance burden.
Would you like me to generate a checklist comparing the vulnerability management requirements of SAQ D versus SAQ A? Or visit Hellgate.io to book a technical demo today.
Latest News

Press Release
May 26, 2026
Hellgate and ConnexPay Partner to Deliver Composable Payment Orchestration and Real-Time Unified Commerce
Tokenization
May 22, 2026
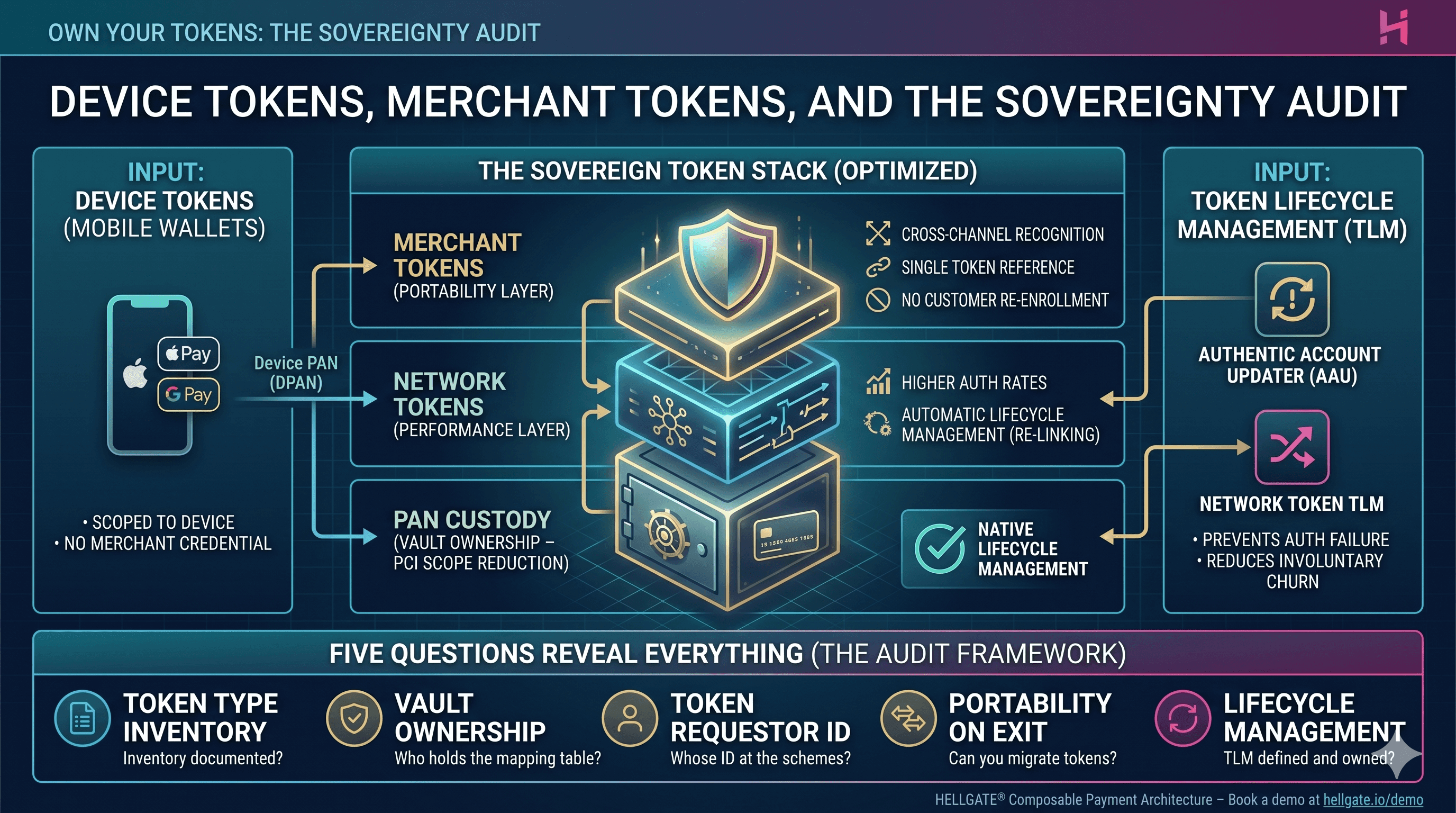
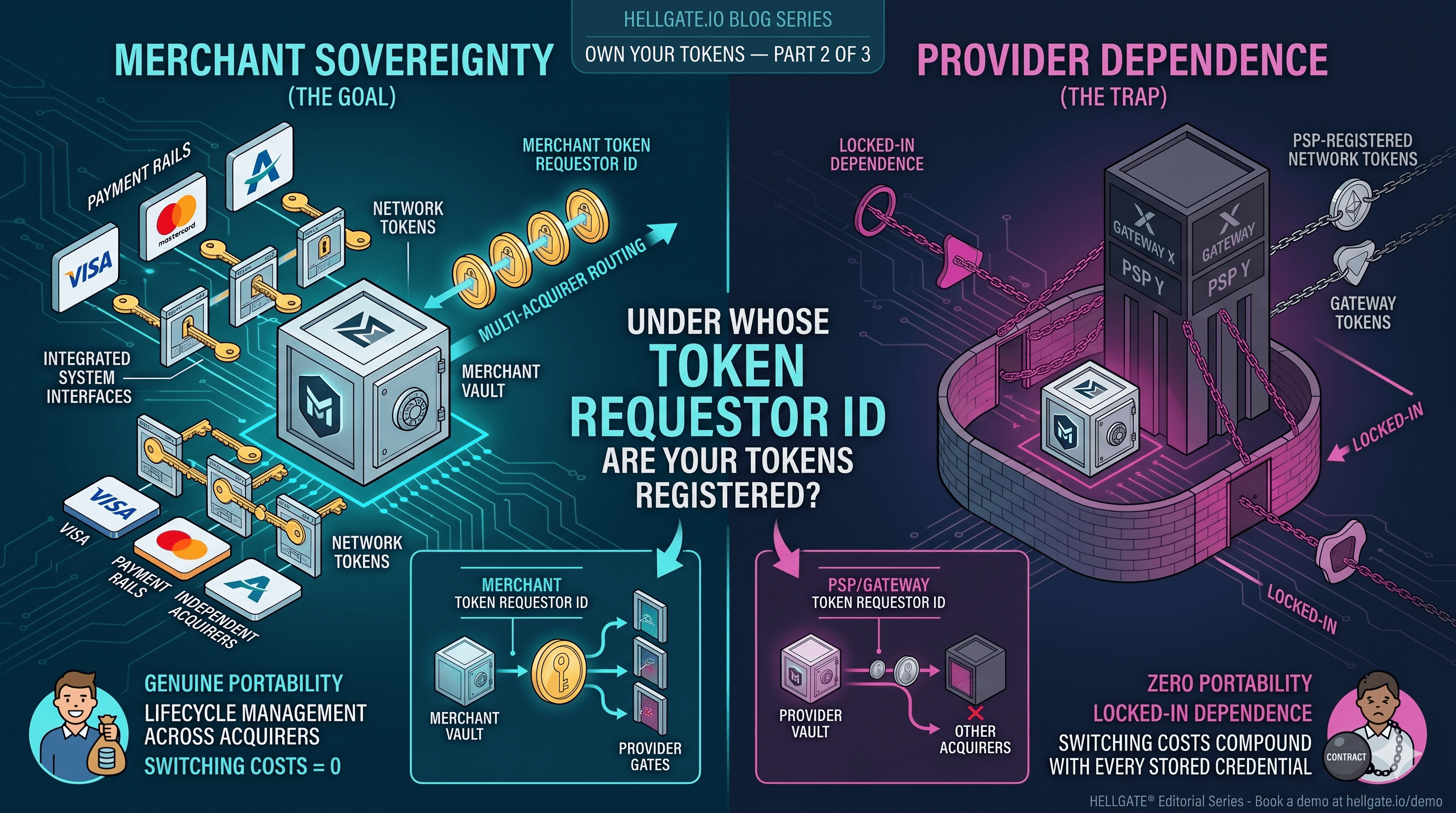
Device Tokens, Merchant Tokens, and the Sovereignty Audit
Tokenization
May 15, 2026